What solutions are we looking for?
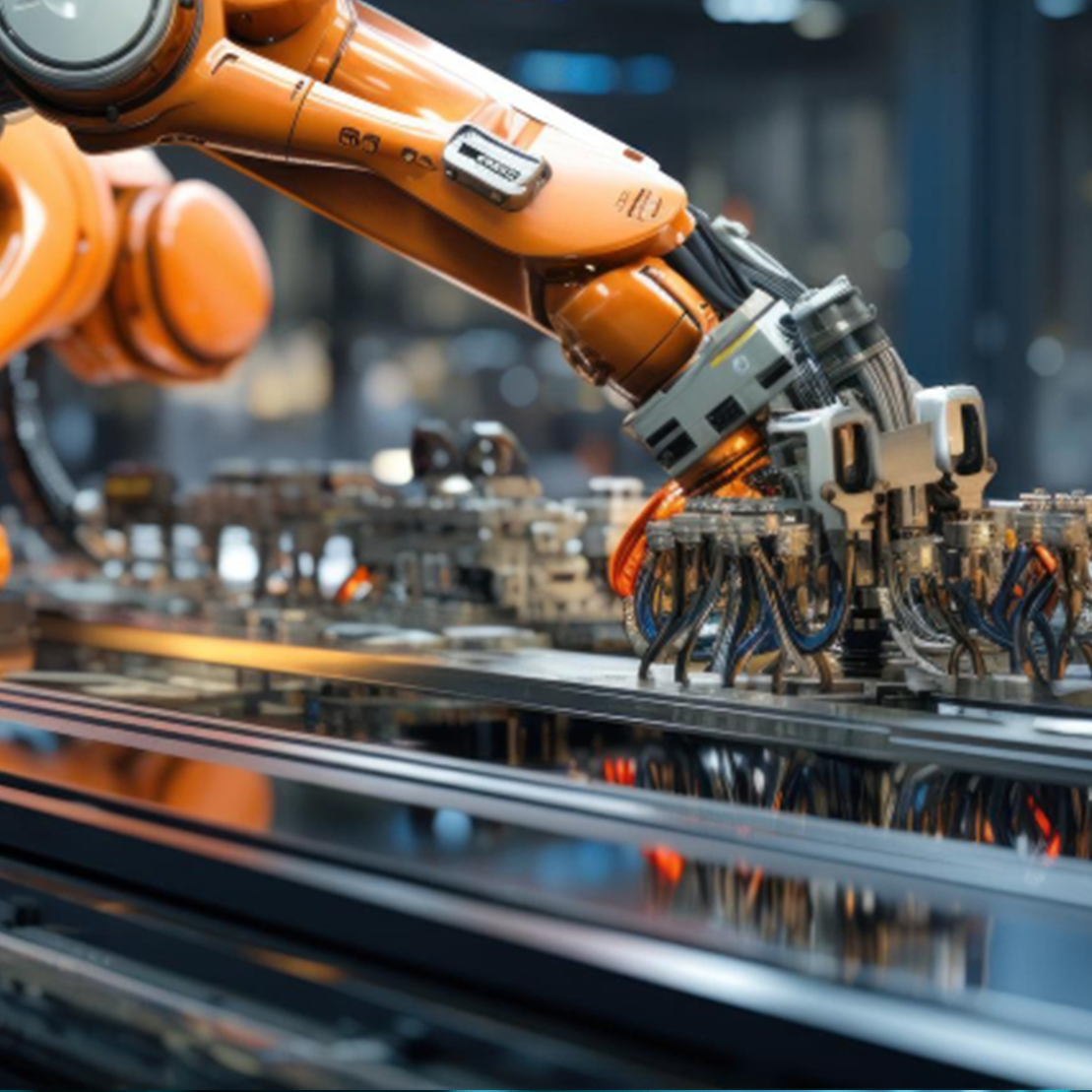
Process automation and robotisation technologies
Solutions should be related to innovative technologies used in automation and robotisation of manufacturing processes and take into account future trends.
Information, communication, and geo-information technologies
The innovation must relate to technologies leading to the development of innovative products, technologies, processes or significant improvements to existing ones.
Smart grids in infrastructures
- Smart cities.
- Smart homes and buildings.
- Smart factories and smart enterprises.
- Smart/intelligent transport systems.
- Smart vehicles.
- Smart grids, such as electricity, heat, fuel, water, sewerage, communications, telecommunications
(including intelligent network management systems).
Closed loop economy
A closed loop economy is a business model that minimises the consumption of resources and the generation of waste. Innovations should fit in with these assumptions.
Cyber security
- Critical infrastructure – securing mission-critical facilities and systems e.g. critical infrastructure facilities, industrial plants etc. Includes protection against physical and cyber-attacks, security of SCADA systems and business continuity in emergency situations.
- Network security – protecting network infrastructure from unauthorised access, attacks or malware. Intrusion Detection Systems (IDS), Intrusion Prevention Systems (IPS), network segmentation, network identity and access management (IAM).
- Internet of things (IoT) – security for smart buildings, protection of industrial equipment. Includes IoT network security, software updates for equipment, encryption of communication, and managing the risks associated with the mass deployment of IoT devices in critical infrastructure.
- Cloud security – data encryption, resilience to DDoS attacks, identity and access management (IAM) for cloud services, control over cloud computing.
- Application security – prevention of sensitive data leaks, SQL Injection, unauthorised privilege escalation, cryptojacking, etc.
- Endpoint security – protecting computers, mobile devices and other endpoints from malware, ransomware and other threats.
- Phishing protection – protection against attacks based on social engineering manipulation, phishing campaigns and spear-phishing.
- Cyber threats related to AI and machine learning.